The inception of blockchain was a 9-page long white paper, “Bitcoin: A Peer-to-Peer Electronic Cash System”, by the pseudo name Satoshi Nakamoto. In the paper, he/she was looking to build a digital currency based on trust-less and distributed consensus.
In the traditional digital payment method, you needed to trust a financial institute as a trusted 3rd party to process your transactions. This 3rd party will maintain a ledger, a record of all transactions, to ascertain each participant’s balance. Since the bank has to incur huge costs on its own, the bank charges for every transaction, making internet commerce expensive. Also, the 3rd party makes the whole system centralised making it a single point of failure. If the 3rd party is compromised, you lose your money.
Instead of this, the system that bitcoin and many other cryptocurrencies use involves giving a copy of this ledger to everyone on the network and everyone on the network maintains this ledger. This system allows transparency, low transaction time, immutability and confidence.
But here the question arises: How to keep the system safe from attackers? Since the ledger is maintained by all nodes on the network, and anyone can join the network, how do we keep an attacker from gaining control? Here comes in Proof-Of-Work.
“Proof of work describes a system that requires a not-insignificant but feasible amount of effort in order to deter malicious uses of computing power”
Now let’s try to understand this with the help of an example. Samay is enrolled to go to school. But there is always a possibility that he misses school and goes to watch a movie with his friends. To know whether Samay really went to school or not his father gives him one sum, that covers all the topics taught in school that day, to solve every day. If Samay is able to solve the sum, his dad knows that he attended school that day and Samay gets a candy bar for being a good boy.
Here, Samay represents a miner (of the respected cryptocurrency), his knowledge (everything done in school that day) is a block of information, the father represents the network with all the other nodes (other miners), the solution to the sum is the Proof-Of-Work that Samay has done that day and the chocolate is the reward the miner gets (usually in the respective cryptocurrency).
Proof-of-work(POW) system is nothing but a mathematical problem, which is moderately hard for the miner to solve but easy to check for the network. This mathematical problem is based on the SHA 256 algorithm and is maintained by coding the prerequisites in the blockchain system. The miners compete to solve this problem. The answer is the proof that they have invested a considerable amount of computing power and hence are designated to be rewarded in the form of bitcoins (or the respected cryptocurrency). This keeps the network safe from attacks and the system running.
To understand how this works practically you need to understand what cryptographic hash functions are:
“A cryptographic hash function is a hash function which takes an input (or ‘message’) and returns a fixed-size alphanumeric string which in no way resembles the ‘message’.”
The string is called the ‘hash value’ or ‘hash’ for short. The ideal hash function has two main properties:
*1. It is extremely computationally difficult to calculate the alphanumeric text (the message) from a given hash.\
- It is extremely unlikely that two slightly different messages will have the same hash.*
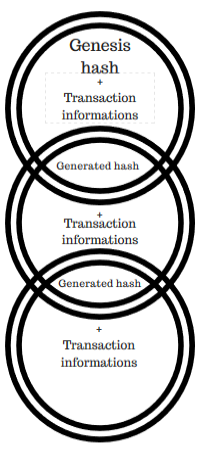
Blockchain Visualized
The process in real life goes something like this. Miners (or nodes in the blockchain network) verify the transactions in block with the copy of the ledger they have. If the transactions check out with previous transactions, they have to put this information along with the hash code of the previous block through a hashing algorithm and obtain the new hash, making a chain of the blocks (hence blockchain). This hashing is the “work” in ‘Proof-of-work”. When this “work” is done successfully the miner is awarded in bitcoins (or the respected cryptocurrency mined).
Generating a hash from a set of information would be trivial for a modern computer, which will again make it easy for an attacker to change the ledger/blockchain. So, in order to make it this process into “work” bitcoin sets a certain level of difficulty. Bitcoin would say that every hash produced should start with a certain number of zeros. This required amount of 0’s are added to the hash by adding a nonce (random alphanumeric) to the information to be hashed.
Let’s say the information block to be hashed is “Hello, world!”. The hashing algorithm used is SHA 256.
“Hello, world!” = > 1312af178c253f84028d480a6adc1e25e81caa44c749ec81976192e2ec934c64
This is the output hash of our block. Now, to make this hashing laborious bitcoin will ask you to add a nonce (the answer to the sum Samay was to solve every day) to the information such that the resultant hash starts with 4 zeros. SHA 256 is a one-sided algorithm, which means it can only give output for an input, but cannot tell the input for an output. So, to get the suitable nonce, one has to use trial and error.
Let’s start adding numbers after “Hello, world!” to eventually get a hashed output that starts with 4 zeros
“Hello, world!0” => 1312af178c253f84028d480a6adc1e25e81caa44c749ec81976192e2ec934c64
“Hello, world!1” => e9afc424b79e4f6ab42d99c81156d3a17228d6e1eef4139be78e948a9332a7d8
“Hello, world!2” => ae37343a357a8297591625e7134cbea22f5928be8ca2a32aa475cf05fd4266b7
.
.
.
“Hello, world!4248” => 6e110d98b388e77e9c6f042ac6b497cec46660deef75a55ebc7cfdf65cc0b965
“Hello, world!4249”=> c004190b822f1669cac8dc37e761cb73652e7832fb814565702245cf26ebb9e6
“Hello, world!4250” => 0000c3af42fc31103f1fdc0151fa747ff87349a4714df7cc52ea464e12dcd4e9
(Notice how the output hash changes entirely even if one character is added. That’s called the avalanche effect)
It would take me 4250 guesses to guess the right nonce. This was a rather simple example. Usually the nonce is an alphanumeric, increasing the combination set.
Now let’s take another example. Max sends Bob 1 Bitcoin. The transaction checks out and is put in the blockchain by a miner. But Max is a real greedy fellow. He thinks of changing the ledger and erasing this transaction. This way he can spend his bitcoin again. He thinks it is really easy. Just go on to the bitcoin network, become a miner, make a block without the transaction and hash it again. No one would ever know. True. No one would ever know if that happens. But, what Max doesn’t understand 3 things:
- He will need a lot of computing power to get the hash to start with,
- Even if he gets that much power, he since he changed the hash of one of the blocks (which is the input for the next block’s hash) he will have to mine all the blocks after the altered block again to get the ledger working again or else the whole system fails and his bitcoin isn’t worth anything.
- To mine all the blocks again and catch up with the rest of the miners means that he has to have more computational power than 51% of the nodes in the networks combined together. That is having the computational power of >75,000 of the world’s biggest supercomputers put together. This becomes economically non-feasible
This is why a distributed consensus ensures the system runs honestly. Till the number of honest nodes are greater than the attacker nodes, the blockchain system remains unbreakable. And That’s how proof-of-work keeps attackers from taking over a cryptocurrency based on blockchain.
When bitcoin was launched, miners used to mine on their PC with their standard CPU. Slowly they realised that the more computational power they have, the higher the chances they have to mine the right nonce first. So, they started using GPU’s as they calculate faster. Today, miners use ASICs (application specific integrated circuits) to mine Bitcoin. Basically, these are purpose built computer chips that are designed to perform SHA256 calculations and do nothing else.
As the miners grow stronger, the bitcoin system keeps increasing the difficulty to mine the hash. This is done by adding another zero in the number of initial zeros. Say if the system requires 20 zeros in the start of a hash, the max steps needed to guess the hash is 220, or 1048576 steps. If the number of zero is increased by 1, that is 21 zeros, the number of maximum stems involved become 221, or 2097152. This is done to keep an average calculation time of 10 minutes constant forever, further making the system robust.
Proof-of-work is the simple yet very efficient way that the power to run a system is distributed among all who use the system. It is what democracy in its truest sense means and is the reason blockchain survives and can empower people.